CFIUS 2.0: ‘Sensitive Personal Data’ in the National Security Context

To better address those concerns and others, Congress gave CFIUS some significant new tools and authorities in 2018 when it enacted the Foreign Investment Risk Review Modernization Act (FIRRMA), modernizing CFIUS’s processes and expanding its jurisdiction to cover so-called non-passive, non-controlling investments in US companies in three focal areas: critical technologies, critical infrastructure, and sensitive personal data. These are minority-position investments, including venture capital and other private equity transactions, through which a foreign person could obtain certain types of governance or information rights with the US company.
Who Should Be Paying Attention to This?
Developments in this area could impact a wide array of US industries that collect or maintain the personal data of Americans and that seek investment from sources that CFIUS might consider to be foreign persons. This could include certain types of companies in the following sectors and areas, just to name a few: financial services, insurance, health care, genetic research and testing, hospitality, travel and tourism, transportation, retail, social media, software, and technology.
Just How Far Will CFIUS Reach Into the Realm of Sensitive Personal Data?
Of the three areas of new CFIUS jurisdiction for minority-position investments, arguably the most novel and potentially far-reaching is transactions involving sensitive personal data. This new type of CFIUS jurisdiction was added to FIRRMA very late in the legislative process, after negotiators from the House of Representatives requested its inclusion. And, it has the potential to significantly alter the investment landscape for data-centric businesses that are seeking capital.
At present, the Treasury Department and other CFIUS member agencies are busy drafting the complex implementing regulations for FIRRMA, carrying out its various mandates and setting the exact scope of CFIUS’s expanded jurisdiction. They have until March of next year to finalize and promulgate those (though CFIUS began test-driving its new authorities late last year). For many years, CFIUS has had the jurisdiction to review “control” transactions (i.e., mergers and acquisitions) involving sensitive personal data, but the new regulations could affect how it analyzes those types of transactions as well.
FIRRMA provided no definition whatsoever for “sensitive personal data,” making it difficult to predict just how broadly or narrowly CFIUS might scope this key jurisdictional term. That is in stark contrast to the new law’s treatment of the two other areas where it expanded CFIUS’s jurisdiction over minority-position investments. FIRRMA laid out at least a basic definition of “critical infrastructure,” as well as a highly detailed definition of “critical technologies.”
What Sort of National Security Risks Was Congress Worried About with Sensitive Personal Data?
Congress stated its concerns regarding sensitive personal data very clearly in FIRRMA (albeit in nonbinding, prefatory language), urging CFIUS to examine the extent to which investments are “likely to expose, either directly or indirectly, personally identifiable information, genetic information, or other sensitive data of United States citizens to access by a foreign government or foreign person that may exploit that information in a manner that threatens national security”.
This helps explain Congress’s rationale for expanding CFIUS’s jurisdiction in this new area, which covers investments by foreign persons in any US company that “maintains or collects sensitive personal data of United States citizens that may be exploited in a manner that threatens national security.” Importantly, only transactions with certain features will trigger this new CFIUS jurisdiction, specifically investments that afford a foreign person: (1) a seat on the US company’s board of directors, the right to observe board meetings, or the right to nominate someone to the board; or (2) involvement in “substantive decisionmaking” of the US company (other than through shareholder voting) pertaining to the “use, development, acquisition, safekeeping, or release” of sensitive personal data of US citizens that the US company collects or maintains.
“Sensitive Personal Data” Vs. “Personally Identifiable Information”
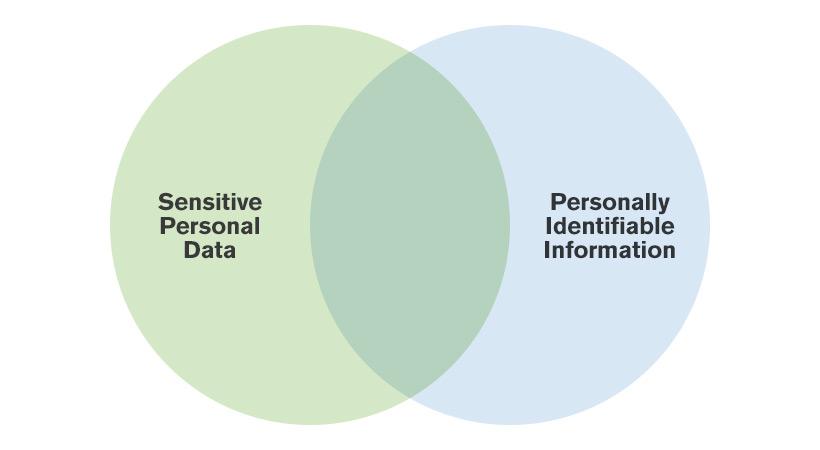
When Congress expanded CFIUS’s jurisdiction in the area of personal data, it opted not to use the term “personally identifiable information” (PII), which has been around for several years and is relatively concrete and specific. Instead, Congress embraced the related term, “sensitive personal data,” giving CFIUS much more latitude to scope its jurisdiction as necessary to target the true national security risks. So, will CFIUS view the terms “sensitive personal data” and PII interchangeable? Probably not. Sensitive personal data is likely to include some, but not all, types of PII. At the same time, the CFIUS definition may include some information that is not considered PII.
The Office of Management and Budget (OMB) defined PII in 2013, by regulation, as: “information that can be used to distinguish or trace an individual's identity, either alone or when combined with other personal or identifying information that is linked or linkable to a specific individual.” The National Institute of Standards and Technology and the Government Accountability Office have offered some helpful examples of PII: name, Social Security number, date and place of birth, mother’s maiden name, biometric records, as well as medical, educational, financial, or employment information.
OMB’s regulations point out that some PII (“public PII”) – such as first and last names, physical addresses, work and home telephone numbers, email addresses, and educational credentials – may be available via phone books, public Internet sites, university listings, and other public sources. The transfer of public PII to foreign persons, via an investment in a US company that has the data, probably does not present heightened national security risks. That type of information is already ubiquitous, so it is less likely to be captured by CFIUS in key definitions in its forthcoming regulations. But other PII may raise significant national security concerns in the eyes of CFIUS and its member agencies and may therefore be included within the scope of the term, sensitive personal data.
To Understand How CFIUS Sometimes Thinks About Personal Data, Use Your Imagination
To assess whether specific types of potentially sensitive personal data could have relevance to national security, it may be a useful exercise to let one’s imagination run wild and consider what a hostile foreign intelligence service (e.g., Chinese or Russian intelligence agencies or their proxies) or a foreign terrorist organization might be able to do with that data. For example:
- Could China’s shadowy Ministry of State Security (MSS) use that data for malign purposes, such as connecting the dots to identify and target a US Government employee who may be operating in some clandestine capacity somewhere in the world?
- Could that data enable Russia’s devious Foreign Intelligence Service (SVR, the successor to the notorious KGB) to exploit a specific vulnerability (e.g., financial trouble or an extramarital affair) of a career US Government employee in the Washington Metropolitan Area who has robust access to high-level classified information, then blackmail or bribe that employee and thereby gain sustained access to sensitive intelligence?
- Could homegrown operatives of the terrorist groups, Hizballah or the Islamic State in Iraq and Syria (ISIS), utilize that data to surreptitiously gain access to a sensitive system or facility, then steal valuable information about US critical infrastructure (e.g., a nuclear power plant) or vital military systems or even sabotage them?
So, How Is CFIUS Likely to Define “Sensitive Personal Data”?
For good reason, CFIUS’s forthcoming rules regarding sensitive personal data are likely to be nuanced, and they will probably place a premium on both the quality and the quantity of the data in question. The definition could cover information such as Social Security numbers, driver’s license numbers, passport information, employee records and tax information, medical records and related data covered by the Health Insurance Portability and Accountability Act (HIPAA) and related laws, genetic or genomic information, ancestry data, biometric information, credit and debit card numbers, bank accounts and other financial information (including transaction history), consumer purchase history, online account information (including account numbers and passwords), Internet history, social media data (non-public only), school records, private personal phone numbers (including mobile numbers), email addresses, geolocation and related data from mobile device software apps, travel plans and history, and data pertaining to intimate personal relationships (including data from dating services).
However, CFIUS may also exercise its discretion to exclude situations where the US company has only limited amounts of these types of data. The CFIUS member agencies are very cognizant of the need to avoid drafting the forthcoming regulations so broadly that the resulting flow of incoming filings would exceed CFIUS’s bandwidth, and those types of considerations will certainly manifest themselves in the regulations.
On the flip side of the coin, CFIUS’s forthcoming definition of sensitive personal data is unlikely to cover information that is readily accessible online or from other public sources, such as names, physical addresses, work and home phone numbers, race, gender, ethnicity, and educational credentials. In reality, because CFIUS has yet to officially clarify which personal data is sensitive and which is not, investors and businesses of all types and sizes will remain somewhat in the dark until the draft regulations are released. However, a handful of noteworthy data breaches, as well as some publicly reported CFIUS cases from recent years, may shed some light on where these regulations are headed. Ultimately, the national security risks are often virtually identical, regardless of whether the sensitive personal data gets acquired through illegal means (e.g., theft) or legal means (e.g., acquiring a company or gaining access to its data via a non-passive minority-position investment).
The OPM Hack and Travel Data – A Counterintelligence Nightmare for the US Government
In 2014, hackers from China penetrated the computer systems of the Office of Personnel Management (OPM) in Washington, DC. The infamous OPM hack, through which the personal data of more than 22 million current and former federal employees was exfiltrated, was one of the most damaging data thefts in the history of the US Government. The lost trove of data included millions of security clearance files, which contained detailed information about applicants, their family members, and their friends; additional personnel records containing Social Security numbers, performance evaluations, and duty assignments; as well as fingerprints, extensive financial and medical records, and computer usernames and passwords.
In the hands of a foreign adversary such as China, this sort of sensitive data on current and former US Government officials is a powerful weapon. The data would be even more useful to a hostile foreign power who can combine it and cross-reference it with detailed travel data on millions of Americans harvested from a vast private database. The unfortunate result is the exact type of national security quandary that the first “use your imagination” scenario above sought to describe.
In the era of artificial intelligence (AI) and data lakes, these are some of the very same considerations that drive decisionmaking by CFIUS regarding the national security risks of permitting a particular foreign person to invest in a US company that collects or maintain sensitive personal data. It is certainly not lost on the CFIUS member agencies that, in a drive to dominate the field of AI globally, China is attempting to fuse AI with big data, frequently involving the unfettered surveillance of its own citizens. Of course, the effectiveness of AI depends on data – both its quantity and its quality – and China has learned to leverage massive pools of data to fuel its quest for AI supremacy. As CFIUS reviews transactions involving the sensitive personal data of Americans, it will seek to prevent that data from falling into the hands of China or other foreign adversaries.
Geolocation Data and Mobile Apps – Strava’s “Heat Map”
Today, a multitude of mobile device apps track users’ locations using GPS technology, then share or even sell that geolocation data to third parties, usually unbeknownst to users. This type of data can reveal not only things like consumer habits, but also data on a person’s general “pattern of life.” That type of information could potentially have great utility for a foreign adversary. So, when transactions inevitably come before CFIUS that involve a US company that collects or maintains this type of geolocation data, they are likely to come under increased scrutiny. CFIUS will work rigorously to ensure that this type of data does not fall into the hands of foreign adversaries, wherever preventable.
Recently, a real-life example illustrated the national security pitfalls of geolocation data. The locations of several American military bases in combat zones (including in Afghanistan, Iraq, and Syria) were revealed after the maker of a fitness-tracking mobile app posted online a “heat map” that marked the locations of its users. Very likely, the app users in those locations were American troops (as well as perhaps civilians supporting their missions) who wore fitness trackers or other mobile devices as they moved around. Soon after, this significant security blunder led the Department of Defense to alter its security policies on the use of mobile devices by deployed troops, as well as for personnel working at the Pentagon.
Genetic and Medical Data – FBI Warnings and the PatientsLikeMe Transaction
Perhaps the most alarming area of personal data is genetic (or genomic) information, including the DNA of US citizens. In 2017, FBI Special Agent Ed You testified before the US-China Economic and Security Review Commission that China has gained “significant access to US genomic data and biological samples through research partnerships, investments, mergers, and acquisitions.” Government officials like Special Agent You are deeply concerned that, in allowing massive sets of US medical and genetic data to be generated and pooled for efforts such as precision medicine, certain vulnerabilities are being simultaneously created. You advocates for assessing the long-term implications of China gaining access to data that is ostensibly to support efforts such as disease research, health diagnostics, and genealogy studies.
At the far end of the risk spectrum, one concern that has been voiced is that a hostile foreign power could get its hands on this same data, including the DNA of US citizens, and utilize it to engineer biological or chemical agents that specifically target certain US Government officials, other individuals, or ethnic groups. Other concerns center on the use of this data to exploit or extort specific individuals’ vulnerabilities for purposes such as those in the three “use your imagination” scenarios above.
CFIUS is clearly taking medical data seriously, as demonstrated earlier this year in a transaction involving Massachusetts-based health-tech startup PatientsLikeMe. The company was reportedly forced by CFIUS to ditch a $100 million majority-stake investment from iCarbonX, a Chinese genetic research firm with machine learning capabilities, due to national security concerns related to patient data. PatientsLikeMe connects patients to others with similar health conditions, and it says its data includes more than 650,000 people with 2,900 different health conditions. As a result, PatientsLikeMe was forced to find a US buyer.
Biometric data – The FaceApp Controversy
With the explosive growth of hacking and general cyber insecurity, biometric identifiers are increasingly being used to verify people’s identities. The most common applications of this cutting-edge technology thus far have centered on security, including everyday tasks such as logging into mobile phones but also controlling access to secure facilities and systems. Of course, biometrics also have clear applications for law enforcement. Some of the most common types of biometric data include fingerprint scans, facial recognition, iris recognition, DNA tests, signature analysis, gait analysis, voice recognition, and hand geometry.
In the national security context, foreign adversaries would have seemingly endless ways to exploit a trove of biometric data. A real-life example of how these risks can manifest themselves recently presented itself with the controversy over the FaceApp mobile app, which was developed by a Russian company. Facial images and other biometric data will likely be of great interest to CFIUS as it scopes its jurisdiction over minority-position investments involving sensitive personal data, and it will surely seek to prevent that data from falling into the hands of foreign adversaries who could use it for malign purposes.
Government Email Addresses – Ardit Ferizi and the ISIS Kill List
One might think that lists of email addresses should be considered pretty harmless, but the Justice Department (which is a CFIUS member agency) may disagree. The case of Ardit Ferizi illustrates what can happen at the intersection of terrorism and the cybertheft of sensitive personal data. Ferizi was a citizen of Kosovo who aided ISIS, over the course of two months in 2015, by penetrating the computer server of an Internet retail company based in Illinois and stealing 100,000 names, Social Security numbers, and credit card records. He culled from the server all the email addresses of US government civilians and military personnel (those ending in “.gov” or “.mil”). Then, he compiled for ISIS a “kill list” of 1,351 American troops or other government employees and passed it directly to a senior ISIS operative.
Ferizi is currently serving a 20-year federal criminal sentence for providing material support to the terrorist group, ISIS, as well as other hacking-related offenses. His case is evidence of how even seemingly innocuous personal data can be misused by nefarious actors, and it goes to show that at least one CFIUS member agency considers lists of email addresses to be sensitive personal data with real national security implications.
Data on Intimate Personal Relationships – The Grindr Transaction
It is also clear that CFIUS has concerns about data relating to intimate personal relationships, such as the information collected and maintained by dating services and related mobile apps. In March of 2019, news reports indicated that Kunlun Tech Co Ltd., a Chinese gaming company, had been pressured by CFIUS to sell the popular US dating app company, Grindr LLC, which it had acquired in two phases (2016 and 2018) for $245 million. Two months later, Kunlun disclosed that it had agreed to CFIUS’s request and had set a 2020 deadline for complying. CFIUS had reportedly raised serious concerns about a Chinese company having access to Grindr’s data on American citizens (which includes information such as its users’ HIV status, dating habits, and sexual orientation) and could be used by China to blackmail Americans in national security-related positions. Reportedly, CFIUS recently dropped its objections to Kunlun’s plan for an initial public offering (IPO), in which Grindr stock would be sold on an exchange outside of China.
Financial Data – The Fortress Investment Group and MoneyGram Transactions
In January of 2018, news broke that CFIUS had killed a $1.2 billion acquisition of MoneyGram, the US financial services company, by Ant Financial, a Chinese financial and mobile payment company affiliated with Chinese e-commerce and technology giant, Alibaba. MoneyGram is the world’s second-largest money transfer company, and CFIUS had reportedly raised objections regarding Chinese entities potentially getting access to the personal data of US citizens, rejecting various proposals to mitigate those concerns.
In 2017, sensitive personal data may have also played a secondary role in the prolonged CFIUS scrutiny of the $3.3 billion acquisition of Fortress Investment Group by the Japanese conglomerate, SoftBank. CFIUS eventually cleared the transaction, but reportedly only after SoftBank agreed to relinquish its involvement in the day-to-day operations of Fortress, a New York-based asset management and private equity investment company. Some had speculated that CFIUS may have had specific concerns with Softbank’s use of Huawei systems, in light of the US Government’s longstanding security concerns about the Chinese telecommunications giant. Such issues would have compounded any concerns about the sensitive personal data of US citizens falling into Chinese hands.
Conclusion
As CFIUS formulates its definition of “sensitive personal data” and scopes its jurisdiction over investments in US companies that collect or maintain it, a wide range of US industries will want to pay close attention. As companies like MoneyGram, Strava, Grindr, and PatientsLikeMe have learned, the national security implications of certain personal data are not always readily apparent. CFIUS is likely to release for comment its draft regulations in the next couple of months, and Arent Fox will continue to closely monitor developments.
This is the fourth client alert in the “CFIUS 2.0” series, which focuses on implementation of the Foreign Investment Risk Review Modernization Act of 2018 (FIRRMA). Dave Hanke was the primary staff architect of FIRRMA and chief strategist behind its 2018 enactment, while working at the Senate Select Committee on Intelligence as the staff designee for Sen. John Cornyn (R-Texas), the lead author of FIRRMA.
For a primer on CFIUS, FIRRMA, and their nexus with forthcoming export controls on emerging technologies, a recent one-hour Lexology webinar is available for free download here.
- Related Industries
- Related Practices
-
Read Time
12Minutes